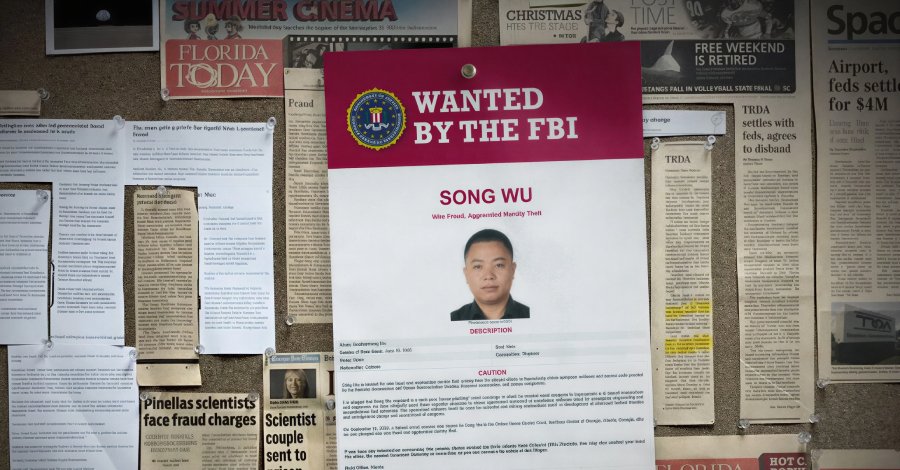
CISA Adds Four Vulnerabilities to KEV List

The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added four vulnerabilities to its catalog of known exploited vulnerabilities (KEV) on Friday. These vulnerabilities affect products from SimpleHelp, Samsung MagicINFO 9 Server, and D-Link DIR-823X routers. CISA cites evidence of active exploitation of these vulnerabilities. The first vulnerability, CVE-2024-57726, has a CVSS score of 9.9 and involves a lack of authorization in SimpleHelp.
This vulnerability allows attackers to gain unauthorized access to sensitive data. CISA warns that this vulnerability is already being actively exploited, underscoring the urgency of an update. The second vulnerability, CVE-2024-57727, affects the Samsung MagicINFO 9 Server. This security flaw enables attackers to execute remote code, potentially leading to a complete compromise of the server. CISA recommends updating the software immediately to minimize the risk of an attack.
The third vulnerability, CVE-2024-57728, pertains to the D-Link DIR-823X router series. This vulnerability allows attackers to take control of the device and use it for further attacks. CISA has also noted active exploitation in this case and recommends updating the firmware to the latest version. The fourth vulnerability, CVE-2024-57729, also affects D-Link routers and has a CVSS score of 8.5. This vulnerability allows attackers to intercept and manipulate traffic.
CISA has urged the affected companies to take immediate action to protect their systems. The agency has set a deadline of May 2026 by which all federal agencies must implement the necessary updates. This measure aims to ensure that government systems are protected against known threats. The agency has emphasized that compliance with this deadline is crucial for national security. The inclusion of these vulnerabilities in the KEV list is part of CISA's efforts to strengthen cybersecurity in the U.S.
The agency has previously taken similar actions to alert organizations to critical security vulnerabilities. CISA encourages companies to take proactive steps to secure their systems. The agency has also provided a range of resources to assist organizations in identifying and addressing these vulnerabilities, including technical guidance and risk mitigation recommendations. CISA stresses that a swift response to these threats is essential to minimize potential damage.
Vulnerabilities have been discovered in recent weeks by various security researchers who informed CISA about the potential risks. The agency then took immediate action to warn the public and inform the affected companies. CISA plans to provide regular updates on security vulnerabilities to enhance transparency. The agency has urged affected companies to review their security protocols and ensure that all systems are up to date. CISA has also emphasized that collaboration between the public and private sectors is crucial for improving cybersecurity.
CISA will continue to work closely with the affected companies to ensure that necessary measures are taken. The vulnerabilities are another example of the growing challenges in the field of cybersecurity. Given the increasing number of cyberattacks, it is essential for companies to continuously review and improve their security measures. CISA will continue to strengthen its role as a central point of contact for cybersecurity information and resources. The agency has urged affected companies to update their systems by May 2026 at the latest to minimize risks.





💬 Comments (0)
No comments yet. Be the first to comment!