Critical SQL Injection Vulnerability in LiteLLM Exploited

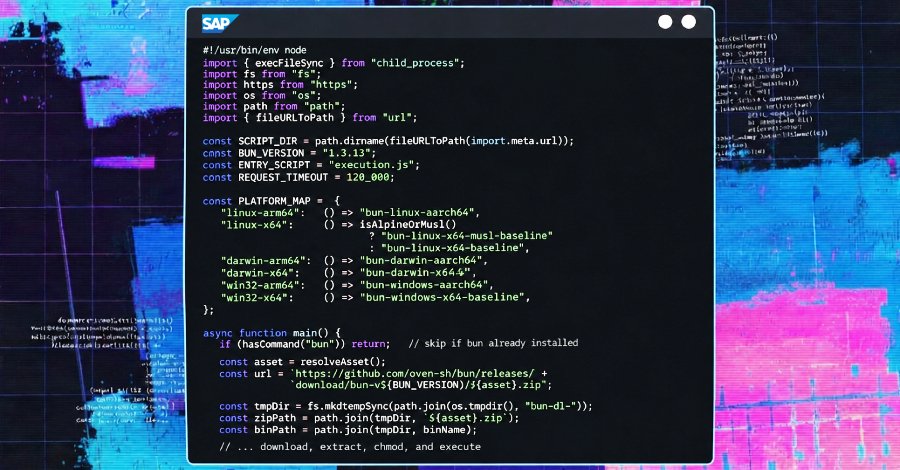
A critical security vulnerability in the LiteLLM Python package from BerriAI, known as CVE-2026-42208, has been actively exploited within 36 hours of its disclosure. This vulnerability, rated with a CVSS score of 9.3, allows for SQL injection, enabling attackers to modify the underlying database. The vulnerability was made public on April 30, 2026. By May 1, 2026, security experts reported the first attacks targeting this vulnerability.
The rapid exploitation of such vulnerabilities is an alarming sign of the response speed of threat actors in today's cyber landscape. LiteLLM is widely used in various applications, increasing the potential reach of the attacks. The vulnerability could allow attackers to steal, manipulate, or even take control of affected systems. Experts warn that the impact on businesses could be significant, especially if sensitive data is involved.
The developers at BerriAI have already announced an update to address the security vulnerability. Users of the LiteLLM package are strongly urged to install the update as soon as possible to protect themselves from potential attacks. However, the exact availability of the patch has not yet been disclosed. The swift exploitation of CVE-2026-42208 is not the first incident of its kind. In the past, similar vulnerabilities have been exploited shortly after their disclosure.
This underscores the need for companies to reassess their security practices and take proactive measures for risk mitigation. The security community has already responded to the threat by disseminating information about the vulnerability and possible countermeasures. Security researchers recommend temporarily suspending the use of LiteLLM in critical applications until the update is available. This could help minimize potential damage. The BerriAI developers are committed to improving the security of their products and have announced plans to implement faster response times to security vulnerabilities in the future.
The community expects the company to learn from this incident and raise security standards. The vulnerability affects not only LiteLLM but also raises questions about the overall security of open-source packages. Many companies rely on this software without fully understanding the potential risks. Experts advise conducting regular security reviews and audits to detect such vulnerabilities early. The CVE-2026-42208 vulnerability could have far-reaching consequences for LiteLLM users, especially in data-dependent industries.
The exact number of affected systems is currently unknown; however, it is estimated that thousands of applications may be at risk. Security research will continue to be pursued intensively to assess the impact of this vulnerability. Experts are working to analyze the attack vectors and develop defense strategies. The situation remains dynamic, and further information is expected. The vulnerability has been registered by the National Vulnerability Database (NVD) and is part of a growing list of security issues arising in software development.
The NVD has classified the vulnerability as critical, emphasizing the urgency of remediation. The BerriAI developers have announced that they will provide an update in the coming weeks to address the vulnerability. Users should regularly check their systems for updates to ensure they are protected against such threats. The CVE-2026-42208 vulnerability is another example of the challenges faced in software development. The rapid exploitation of such vulnerabilities requires constant vigilance and adaptation of security strategies.
The security community will continue to work closely together to minimize the impact of this and similar vulnerabilities. The need for robust security practices is becoming increasingly clear, especially at a time when cyberattacks are becoming more complex. The vulnerability has been ranked by security experts as one of the most critical this year, underscoring the urgency of remediation. The CVSS rating of 9.3 indicates that the threat must be taken seriously. It was published in April 2026 and has already led to a variety of attacks targeting the vulnerability.








💬 Comments (0)
No comments yet. Be the first to comment!