New Ransomware Vect 2.0 Threatens Data Integrity

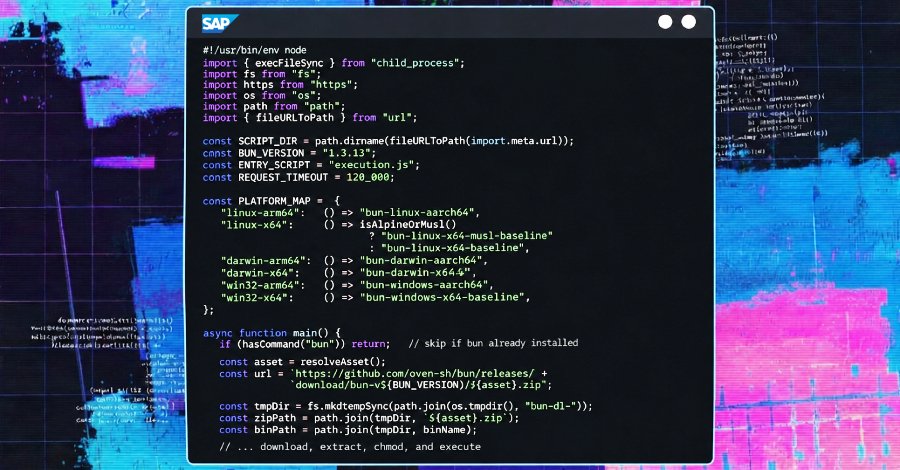
Check Point has issued a warning in a recent report about the new ransomware Vect 2.0, which has rapidly spread in recent months. This malware fundamentally differs from traditional ransomware programs, as it permanently destroys encrypted data. Users who pay the demanded ransom cannot recover their files, making Vect 2.0 a particularly dangerous threat. The operation of Vect 2.0 is alarming. While the program generates a key for data recovery, this key is immediately deleted once the data size exceeds 131 KB.
This means that attackers are unable to deliver what they promise, undermining the motivation to pay the ransom. Experts therefore refer to Vect as a "data destroyer" with an attached ransom demand. The ransomware is not limited to a specific operating system. According to Check Point, both Windows, Linux, and ESXi systems are vulnerable to attacks by Vect 2.0. The spread often occurs through infected links embedded in emails or on websites.
This method is part of a larger network of "ready-made" malware distributed through illegal channels. Oskar Rödin, a security expert at Check Point, emphasizes the need for proactive protection. Recommended measures include using reliable antivirus programs and regularly creating robust backups. These steps are crucial to defend against threats posed by Vect 2.0 and similar malware. The warning about Vect 2.0 comes at a time when cyberattacks are increasing worldwide.
According to the Cybersecurity Report 2026, there was a 45% increase in ransomware attacks in the first quarter of 2026 compared to the previous year. This increase highlights the urgency of strengthening security measures and staying informed about current threats. The security situation is exacerbated by the fact that many businesses and individuals still tend to pay ransoms when affected by ransomware. However, experts warn that this can lead to further attacks in the long run. Paying ransoms encourages attackers to continue their activities and develop new variants of malware.
To protect against Vect 2.0, users should be particularly vigilant about suspicious links and attachments. These can appear in both personal and business emails. It is recommended to report or mark suspicious messages as spam immediately before deleting them. Raising awareness of such threats is an important step towards improving cybersecurity. The development of Vect 2.0 shows that cybercriminals are constantly developing new methods to achieve their goals.
The combination of data destruction and ransom demand represents a new dimension of threat that affects both businesses and individuals alike. Security authorities and IT experts are working to develop strategies to counter such threats. Check Point recommends always installing the latest security updates to protect systems from known vulnerabilities. Regular training for employees in companies can also help raise awareness of cyber threats and improve responsiveness in the event of an attack. The ransomware Vect 2.0 is an example of the ever-evolving landscape of cyber threats. The need to continuously stay informed about new attacks and security measures is essential. According to Check Point, the first reports of Vect 2.0 emerged in January 2026.








💬 Comments (0)
No comments yet. Be the first to comment!